Description
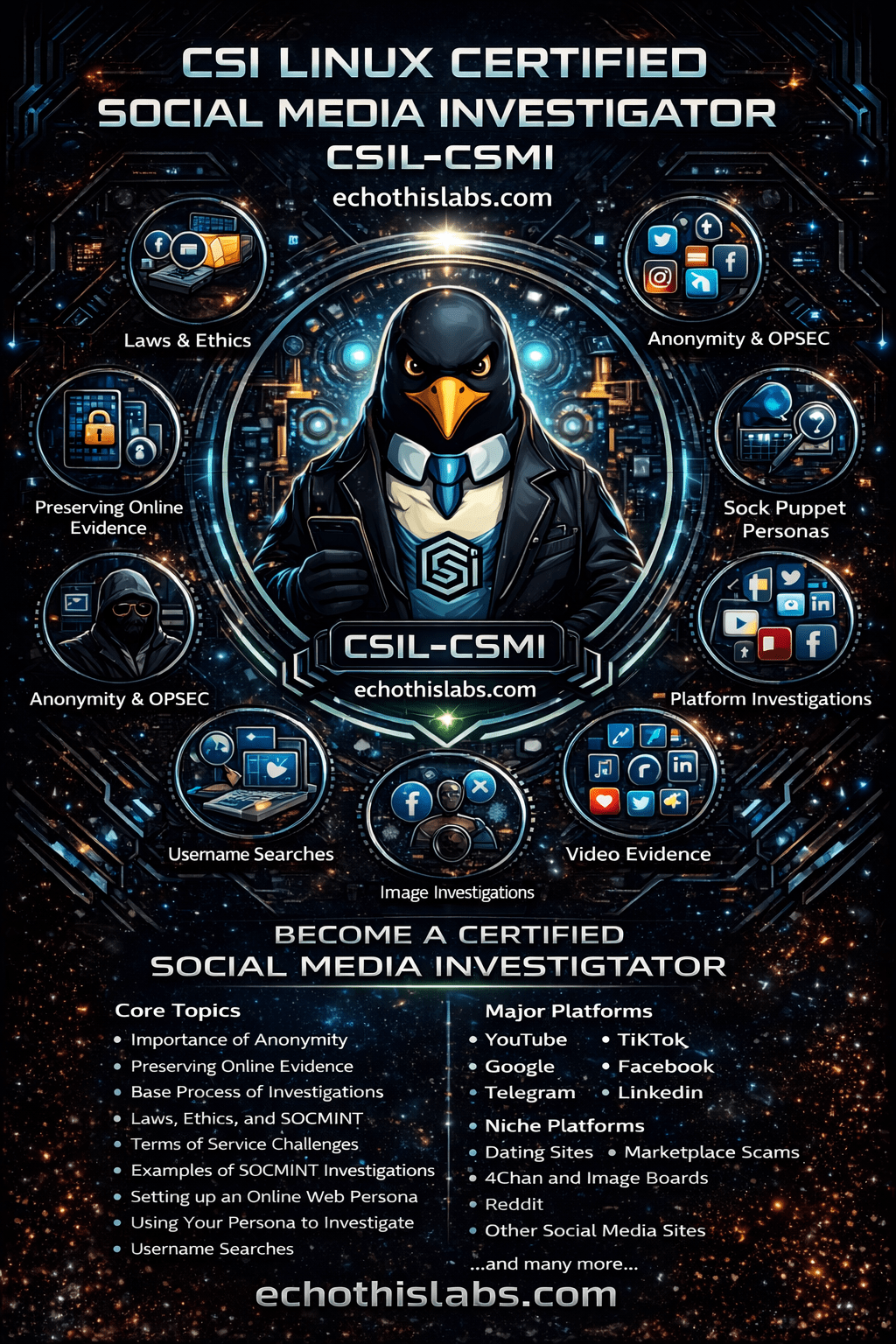
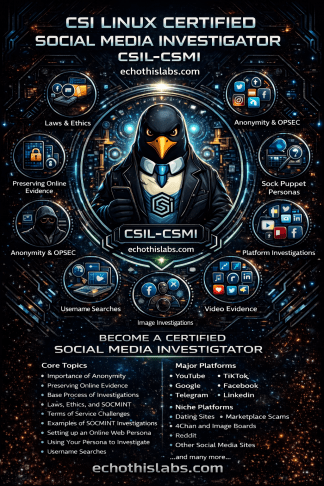
In today’s interconnected world, digital trails on social media platforms often hold the keys to unraveling mysteries. The CSI Linux Certified Social Media Investigator course illuminates the art and science of this essential investigative realm. Dive deep into the intricacies of data collection, unravel the narratives from vast social media landscapes, and learn to craft reports that provide actionable intelligence and stand robust in the courtrooms.
Whether piecing together a puzzle starting with the slender thread of probable cause or delivering vital insights to decision-makers, the CSIL-CSMI certification equips you with the tools and techniques to excel. Step into the vanguard of social media investigations and make every digital clue count.
- Law Enforcement
- Intelligence Personnel
- Private Investigators
- Insurance Investigators
- Cyber Incident Responders
- Digital Forensics (DFIR) analysts
- Penetration Testers
- Social Engineers
- Recruiters
- Human Resources Personnel
- Researchers
- Investigative Journalists
- OPSEC — 13%
- Technology and Dar Web Basics — 20%
- Laws, Ethics, and Investigations — 9%
- Identification — 16%
- Collection & Preservation — 13%
- Examination & Analysis — 13%
- Online testing
- 85 questions (Multiple Choice)
- 2 hours
- A minimum passing score of 85%
- Cost: $385
The certification is valid for a period of three years. To receive a free retest voucher within this period, you must either:
- Submit a paper related to the subject you were certified in, ensuring it aligns with the course material.
- Provide a walkthrough on a tool not addressed in the original course but can be a valuable supplement to the content.
This fosters continuous learning and allows for enriching the community and the field. Doing this underscores your commitment to staying updated in the industry. If you don’t adhere to these requirements and fail to recertify within the 3-year timeframe, your certification will expire.
The CSIL-CSMI introduces investigators to social media intelligence as a structured investigative discipline focused on anonymity, evidence preservation, lawful collection, platform-aware analysis, persona-driven inquiry, and clear reporting. The module order is arranged to move investigators from foundational investigative safeguards into platform-specific collection, niche social environments, and practical reporting.
This sequence reflects the published CSIL-CSMI focus on social media intelligence, OPSEC, collection and preservation, platform-specific investigative techniques, and examination and analysis. It also aligns with the intended audience described in the course document, including law enforcement, intelligence personnel, private investigators, insurance investigators, DFIR analysts, cyber responders, recruiters, human resources personnel, researchers, and investigative journalists.
- Introduction: Opens the course, frames the social media investigative mission, and prepares investigators for the progression from collection to courtroom-ready reporting.
- About the CSIL-CSMI: Defines the certification purpose, scope, audience, and how the course supports real-world social media investigations.
- Importance of Anonymity: Introduces investigator safety, compartmentation, attribution risk, and the operational reasons anonymity must be established early.
- Preserving Online Evidence: Places preservation at the front of the workflow so investigators learn to capture fragile online evidence before content changes or disappears.
- Base Process of Investigations: Establishes the repeatable investigative workflow that ties collection, examination, analysis, and reporting into a defensible process.
- Laws, ethics, and SOCMINT: Adds the legal and ethical guardrails needed before investigators interact with platforms, accounts, or subjects.
- Terms Of Service Challenges: Follows the legal foundation by addressing platform-specific restrictions, access risks, and operational limits investigators must understand before collection.
- Examples of SOCMINT Investigations: Shows how real investigative scenarios unfold so investigators can connect the foundational rules to practical casework.
- Setting up an Online Web Persona – Sock Puppet: Introduces persona creation after the legal and operational groundwork is established, allowing investigators to build a controlled online presence safely.
- Using your persona to investigate: Builds directly on persona creation by showing how to apply the account in a measured investigative workflow without contaminating the case.
- Username Search: Provides a practical entry point for identification and account discovery across social platforms and related services.
- Online Investigations With Images: Expands the investigation into image-based discovery, attribution, context building, and evidentiary collection.
- Video Evidence Collection: Builds on image-based work by covering the collection and preservation of moving-image evidence from social platforms and hosted services.
- 3rd Party Commercial Apps: Introduces supplemental commercial tooling after investigators understand the core workflow, helping them compare native methods with external capabilities.
- YouTube: Focuses on channel analysis, video-source context, comments, metadata opportunities, and preservation concerns unique to the platform.
- TikTok: Examines short-form video investigations, profile analysis, repost behavior, trends, and evidentiary considerations tied to the platform.
- Google: Places search and account-adjacent discovery in the middle of the workflow because investigators routinely use Google to expand leads across the social ecosystem.
- Facebook: Covers profile, group, page, event, and marketplace-adjacent investigative opportunities in one of the most common social environments.
- Telegram: Introduces channel, group, and messaging-based investigation with attention to anonymity, collection, and platform-specific challenges.
- LinkedIn: Shifts into professionally oriented social intelligence where employment history, affiliations, and organizational context can support attribution.
- X – Twitter: Addresses rapid-update social intelligence, account tracking, post analysis, and trend-driven investigative leads on a high-velocity platform.
- X/Twitter and Instagram: Bridges cross-platform investigative patterns by comparing how social identity, content reuse, and behavioral signals can be tracked between major networks.
- Dating Sites: Introduces relationship-driven investigative environments where deception, grooming, fraud, and identity manipulation are common concerns.
- Marketplace Scams: Expands the course into transaction-focused social investigations involving fraud indicators, seller behavior, victim interaction, and evidentiary preservation.
- 4Chan and Image Boards: Covers fast-moving anonymous or pseudonymous communities where content volatility and cultural context are central to interpretation.
- Reddit: Examines threaded community-based investigation, user history, moderation structures, and subreddit-specific context.
- Other Social Media Sites: Closes the platform section by preparing investigators to adapt the same investigative logic to emerging or less common networks.
- Writing the Report: Follows the collection and analysis phases so investigators can convert findings into clear, defensible reporting and actionable intelligence.
- Case Studies: Uses realistic scenarios to reinforce the full investigative arc from planning and collection to analysis and documentation.
- Practicing OSINT and Resources: Ends the map with continued-practice guidance and resources so investigators can keep building skill after completing the formal course.