Description
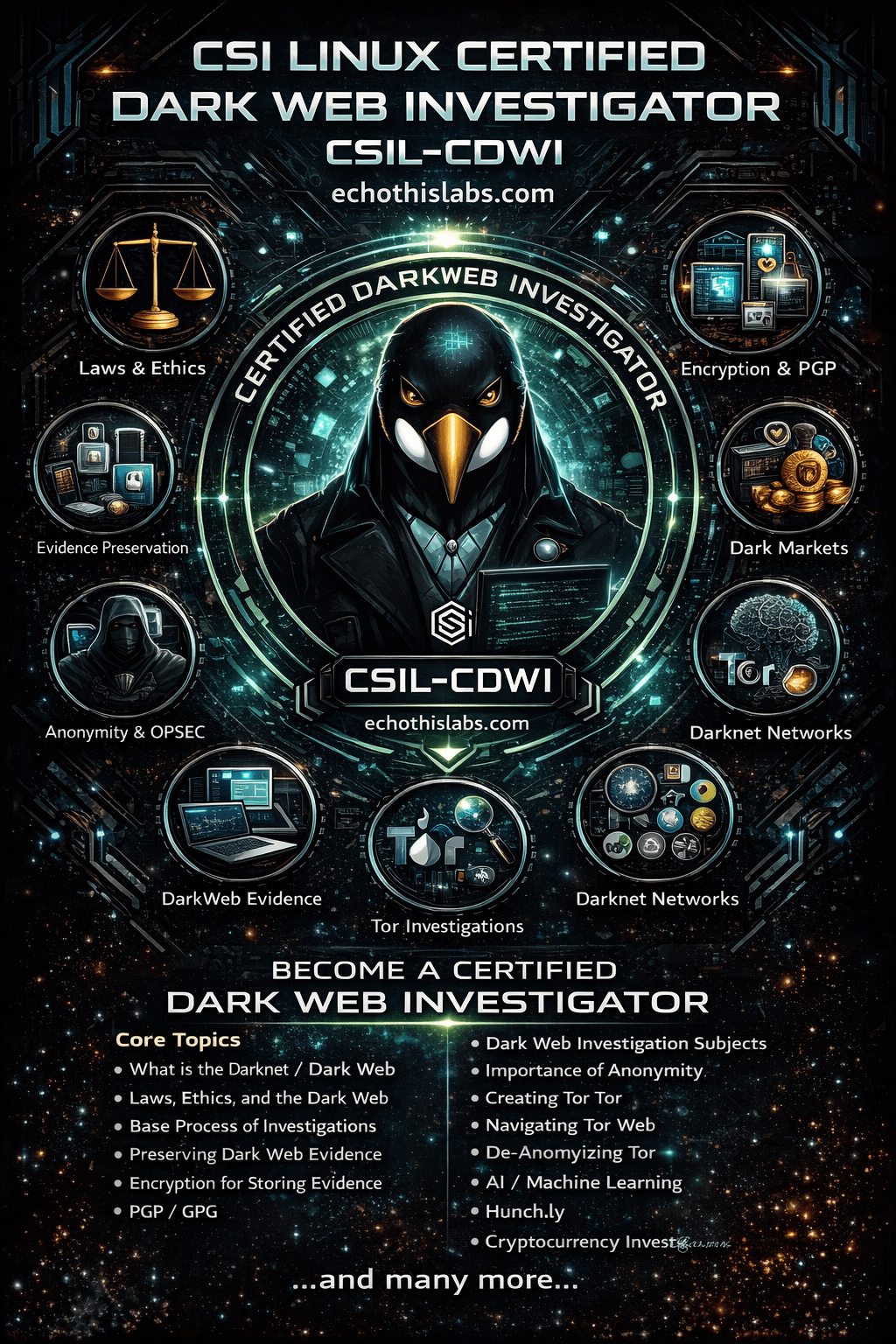
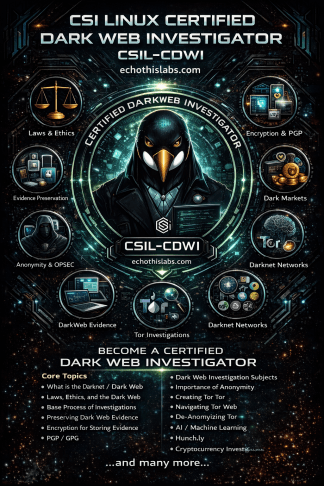
Embark on an intriguing exploration beyond the visible web with the CSI Linux Certified Dark Web Investigator course. Harness the power of the CSI Linux platform to navigate the hidden recesses of unindexed servers, employ advanced search techniques, and confidently collect and analyze data. Tailored to run across Windows, Mac OS, or Linux, this self-contained environment ensures robust digital protection, preventing data cross-contamination. Whether it’s a crucial online investigation or gathering pivotal evidence, arm yourself with CSIL-CDWI expertise, showcasing your ability to provide actionable intelligence and court-ready evidence in the ever-evolving digital realm.
Today’s world demands digital proficiency, and investigations are no exception. Whether it’s securing that pivotal probable cause or delving deeper into intricate online narratives, the CSIL-CDWI certification stands as a testament to your expertise. Stand out in the crowd, deliver actionable intelligence, and present court-ready evidence. Your journey into the dark web begins here.
- Law Enforcement
- Intelligence Personnel
- Private Investigators
- Insurance Investigators
- Cyber Incident Responders
- Digital Forensics (DFIR) analysts
- Penetration Testers
- Social Engineers
- Recruiters
- Human Resources Personnel
- Researchers
- Investigative Journalists
- OPSEC — 13%
- Technology and Dark Web Basics — 20%
- Laws, Ethics, and Investigations — 9%
- Identification — 16%
- Collection & Preservation — 13%
- Examination & Analysis — 13%
- Presentation & Reporting — 14%
- Online testing
- 85 questions (Multiple Choice)
- 2 hours
- A minimum passing score of 85%
- Cost: $385
The certification is valid for a period of three years. To receive a free retest voucher within this period, you must either:
- Submit a paper related to the subject you were certified in, ensuring it aligns with the course material.
- Provide a walkthrough on a tool not addressed in the original course but can be a valuable supplement to the content.
This fosters continuous learning and allows for enriching the community and the field. Doing this underscores your commitment to staying updated in the industry. If you don’t adhere to these requirements and fail to recertify within the 3-year timeframe, your certification will expire.
The CSIL-CDWI introduces investigators to dark web operations as a structured investigative discipline focused on anonymity, evidence preservation, secure handling, hidden-service navigation, alternative darknet ecosystems, cryptocurrency awareness, and defensible reporting. The module order is arranged to move investigators from foundational legal and operational safeguards into persona use, network-specific access methods, evidence collection, advanced tradecraft, and final reporting.
This sequence reflects the published CSIL-CDWI focus on dark web basics, OPSEC, collection and preservation, examination and analysis, and presentation and reporting. It also aligns with the intended audience described in the course document, including law enforcement, intelligence personnel, private investigators, insurance investigators, DFIR analysts, cyber incident responders, penetration testers, social engineers, recruiters, human resources personnel, researchers, and investigative journalists.
- Introduction: Opens the course, frames the dark web investigative mission, and prepares investigators for the progression from access and preservation to courtroom-ready reporting.
- About the CSIL-CDWI: Defines the certification purpose, scope, audience, and how the course supports real-world dark web investigations.
- Getting Started: Gives investigators the initial setup mindset, workflow expectations, and practical entry point into the training environment.
- What is the Darknet/Dark Web: Establishes the core concepts, terminology, and distinctions investigators must understand before moving into operational tradecraft.
- Laws, Ethics, and the Dark Web: Adds the legal and ethical guardrails required before investigators begin collection, access hidden services, or engage with dark web subjects.
- Base Process of Investigations: Establishes the repeatable investigative workflow that ties planning, collection, examination, analysis, and reporting into a defensible process.
- Preserving Dark Web Evidence: Places preservation early so investigators learn to capture volatile hidden-service evidence before content changes, disappears, or becomes inaccessible.
- Encryption for Storing Evidence: Introduces secure evidence handling after preservation so collected material remains protected, controlled, and defensible.
- PGP-GPG: Builds on secure storage by teaching the practical cryptographic concepts investigators encounter when protecting communications, files, and investigative workflows.
- Dark Web Investigation Subjects: Provides the subject-matter categories investigators are likely to encounter so they understand the operational context before entering hidden environments.
- Importance of Anonymity: Introduces investigator safety, compartmentation, attribution risk, and the operational reasons anonymity must be established before active dark web work begins.
- Setting up a Dark Web Persona: Follows anonymity by showing how to build a controlled investigative presence that supports access and interaction without contaminating the case.
- Connecting to Tor: Provides the practical access method most investigators will use first and establishes the baseline for entering dark web environments safely.
- Navigating the Dark Web (Tor): Builds directly on Tor access by showing how investigators move through hidden services, interpret content, and collect leads in context.
- Creating a Tor Hidden Service: Adds deeper technical understanding of hidden-service architecture so investigators better understand how subjects operate and how services are exposed.
- I2P: Introduces investigators to a major non-Tor darknet so the course does not treat Tor as the only hidden network of investigative value.
- I2p EPSITE: Builds on I2P by focusing on site-hosting concepts and the way investigative opportunities differ from standard Tor hidden services.
- Lokinet: Expands the investigator’s view of modern anonymity networks and reinforces the need to adapt workflows beyond Tor.
- Freenet: Introduces decentralized and persistence-focused darknet concepts that differ from more common hidden-service environments.
- Zeronet: Adds a peer-to-peer content model so investigators understand another way hidden or resilient content can be published and maintained.
- Other Onion Routing Dark Nets: Closes the core network section by preparing investigators to transfer the same logic to emerging or less common hidden networks.
- Darknet / Dark Web Evidence: Centers the investigation on what can be collected, documented, attributed, and preserved from hidden-service environments.
- Video Evidence: Builds on web-based collection by addressing the preservation and handling of moving-image evidence encountered on dark web services.
- Dark Markets: Introduces high-risk market environments where investigators must combine OPSEC, preservation discipline, and subject-matter awareness.
- Hunch.ly: Adds workflow-support tooling after the collection foundation is in place, helping investigators document navigation, preserve context, and maintain defensible records.
- What is Cryptocurrency: Provides the monetary context investigators need because dark web services and markets frequently intersect with cryptocurrency-based transactions.
- De-Anonymizing Tor: Introduces higher-risk advanced concepts only after investigators understand anonymity, access, preservation, and baseline collection workflows.
- AI – Machine Learning: Places emerging analytical support near the advanced section so investigators first understand the underlying tradecraft before applying automation or modeling concepts.
- Writing the Report: Follows collection and analysis so investigators can convert findings into clear, defensible reporting and actionable intelligence.
- Reporting Agencies: Extends reporting into escalation and coordination by identifying how findings may be referred, shared, or actioned through the proper channels.
- More Case Studies: Ends the map with applied scenarios that reinforce the full investigative arc from preparation and access to evidence handling, analysis, and reporting.