Description
Unlock a FREE cybersecurity certification on us. Have you ever wondered how CSI Linux differentiates itself from other Linux distributions? This is your chance to dive in.
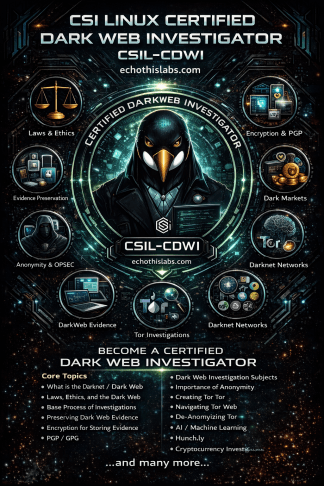
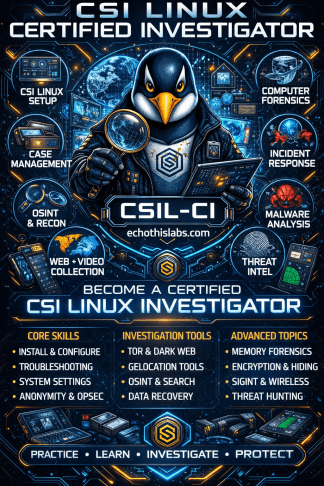
CSI Linux emerges as a pivotal platform for cyber investigations in the contemporary digital landscape. The CSI Linux Certified Investigator (CSIL-CI) is not merely a certification, it is a gateway to understanding and leveraging CSI Linux for investigative purposes. Engage directly with the platform’s specialized features and immerse yourself in the customized tools designed specifically for investigations.
Elevate your skills with the CSIL-CI. This course offers a curated journey through CSI Linux, where you’ll navigate areas like Case Management, Online Investigations, and Computer Forensics. Understand how to approach challenges like Malware Analysis, Encryption, and the nuances of the Dark Web, all within the CSI Linux environment.
- Law Enforcement
- Intelligence Personnel
- Private Investigators
- Insurance Investigators
- Cyber Incident Responders
- Digital Forensics (DFIR) analysts
- Penetration Testers
- Social Engineers
- Recruiters
- Human Resources Personnel
- Researchers
- Investigative Journalists
- CSI Linux Fundamentals — 20%
- System Configuration & Troubleshooting — 15%
- Basic Investigative Tools in CSI Linux — 18%
- Case Management & Reporting — 14%
- Case Management & Reporting — 14%
- Encryption & Data Protection — 10%
- Further Analysis & Advanced Features — 7%
- Online testing
- 85 questions (Multiple Choice)
- 2 hours
- A minimum passing score of 85%
- Cost: FREE
The certification is valid for a period of one year.
The CSIL-CI introduces investigators to CSI Linux as a practical platform for case management, online evidence collection, computer forensics, incident response, and specialized investigative analysis. The module order is structured to move investigators from platform orientation and operational readiness into collection, analysis, advanced technical tradecraft, and finally intelligence-driven investigative support.
This sequence reflects the published CSIL-CI focus areas, including CSI Linux fundamentals, system configuration, case management and reporting, investigative tools, encryption and data protection, and further analysis features described in the course outline and exam domains. It also aligns with the intended audience of law enforcement, intelligence personnel, private investigators, DFIR analysts, cyber responders, recruiters, human resources personnel, researchers, and investigative journalists.
- Introduction: Opens the course, establishes the investigative mindset, and frames how CSI Linux supports real-world cyber and digital investigations.
- About the CSI Linux Certified Investigator (CSIL CI): Defines the certification purpose, scope, expected outcomes, audience, and how the course ties into the exam and broader CSI Linux ecosystem.
- Starting the Training: Sets expectations for course navigation, training workflow, lab preparation, and how investigators should move through the material.
- Downloading and installing CSI Linux: Gives investigators a reliable starting point by ensuring the operating environment is correctly acquired and installed.
- Setting up CSI Linux: Builds the baseline workstation configuration needed before investigative work begins.
- Troubleshooting: Places support and recovery early so investigators can resolve setup or platform issues before moving into operational tasks.
- System Settings: Covers the system configuration details that directly affect stability, usability, and investigative readiness.
- The Case Management System: Introduces the operational backbone for organizing cases, preserving records, and managing investigative work inside CSI Linux.
- Case Management Report Template: Follows case management so investigators learn to document findings using the same environment in which they collect and organize evidence.
- Importance of Anonymity: Placed before online collection to reinforce investigator safety, operational security, and attribution risk before active internet work begins.
- OSINT: Provides the investigative framework for collecting and assessing open-source information.
- Communications Tools: Introduces the tools investigators may use to communicate, coordinate, or compartment investigative activity within an operational workflow.
- Connecting to Tor: Builds on anonymity and OSINT by preparing investigators for privacy-conscious online access and dark web adjacent workflows.
- Website Collection: Teaches investigators to capture and preserve web-based evidence in a structured manner.
- Online Video Collection: Expands collection beyond static web content into streaming and hosted video evidence.
- Geolocation: Builds from collected online artifacts into location-focused investigative analysis and attribution support.
- 3rd Party Commercial Apps for Online Investigations: Introduces supplemental commercial tooling after the CSI Linux-native workflow is understood, helping investigators compare native versus external capabilities.
- Computer Forensics: Transitions from online evidence handling into host-based forensic acquisition and examination.
- Data Recovery: Naturally follows computer forensics because investigators often need to recover deleted, damaged, or partially accessible data during examinations.
- Incident Response: Expands from examination into active response workflows where triage, containment, and rapid evidence preservation are critical.
- Memory Forensics: Builds on incident response by focusing on volatile evidence that is often central to live-response investigations.
- Malware Analysis: Follows memory and host analysis because malicious code review is often informed by prior triage and forensic findings.
- Encryption and Data Hiding: Addresses protected, concealed, or intentionally obscured evidence once investigators understand the core forensic workflow.
- SIGINT, SDR, and Wireless: Introduces specialized collection and analysis areas that expand CSI Linux beyond standard workstation and web investigations.
- Threat Intelligence: Shifts from case-specific analysis to intelligence production, contextual awareness, and investigative enrichment.
- Threat Hunting: Builds on threat intelligence by applying intelligence to proactive detection and hypothesis-driven investigative activity.
- Extra tools for practice or starting an investigation: Closes the map with supplemental tools that help investigators continue practicing, expand capability, and launch future investigations efficiently.