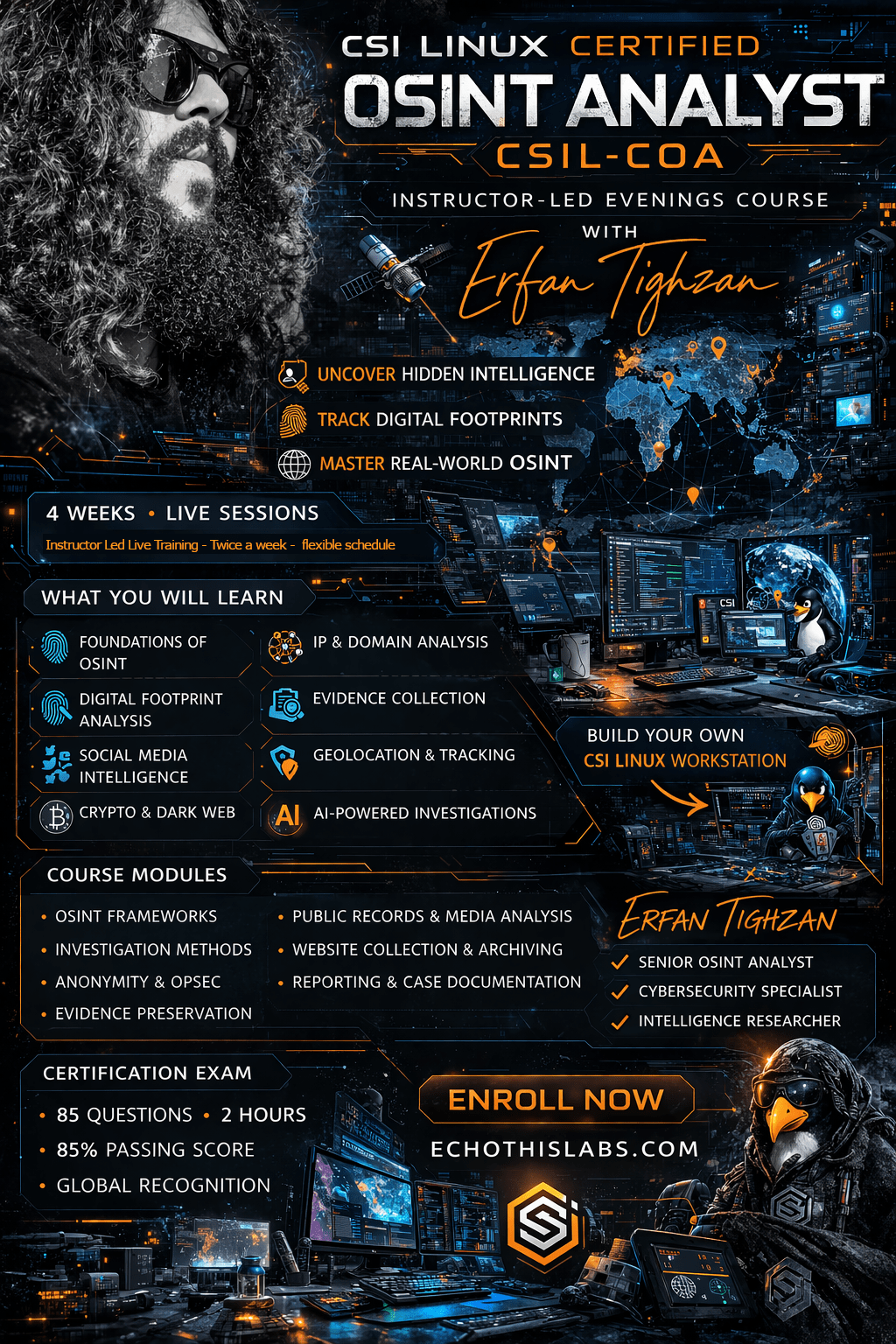
Weekend OSINT Masterclass!
The CSI Linux Certified OSINT Analyst course and certification is designed to teach investigators how to collect, preserve, analyze, and report publicly available information in a way that is structured, lawful, and operationally sound. It covers the lifecycle of an online investigation, from foundational OSINT concepts and pre investigation preparation through anonymity, persona development, online collection, domain and phone analysis, social media, image and video evidence, geolocation, tracking changes, misinformation, AI challenges, cryptocurrency, and final reporting. Its purpose is not to teach random internet searching. Its purpose is to teach how to turn open sources into actionable intelligence that can support real investigations and real decisions.
This course is useful because modern investigations increasingly begin online, long before traditional evidence is collected. For law enforcement, intelligence personnel, private investigators, cyber responders, DFIR analysts, journalists, HR professionals, recruiters, researchers, and related professionals, the course provides a disciplined framework for identifying online leads, preserving digital evidence, avoiding attribution mistakes, protecting operational security, and converting findings into clear reporting. The certification is built around core domains such as OPSEC, technology basics, laws and ethics, identification, collection and preservation, examination and analysis, and reporting.
Phase 1. Orientation, Scope, and Foundations of OSINT
• Module 1. Introduction: Opens the course and frames the role of OSINT in modern investigations.
• Module 2. About the CSIL COA: Defines the certification, course scope, and expectations.
• Module 3. Pre-Training: Prepares the investigator for how to approach the course and build readiness before deeper work begins.
• Module 4. What is OSINT?: Establishes the meaning, value, and limitations of open source intelligence.
• Module 5. Examples of Online Investigation: Shows how OSINT appears in real investigative contexts and why it matters operationally.
Phase 2. Legal, Ethical, and Operational Preparation
• Module 6. Laws, Ethics, and OSINT: Covers legal boundaries, ethical obligations, and disciplined investigative conduct.
• Module 7. Importance of Anonymity: Explains why investigator protection and source separation matter in online work.
• Module 8. IP Addresses, Proxies, and VPNs: Builds technical understanding of online infrastructure, attribution risk, and anonymity support.
• Module 9. Crafting Your Digital Disguise: The Art of Persona (Sock Puppet) Creation: Teaches how to create a believable investigative persona.
• Module 10. Using your persona to investigate: Moves from persona creation to lawful and disciplined operational use.
Phase 3. Collection, Preservation, and Online Source Handling
• Module 11. Preserving Online Evidence: Covers evidence preservation, documentation, and defensible capture of online material.
• Module 12. Website Collection: Focuses on collecting websites and related online artifacts in a structured manner.
• Module 13. DNS, Domains, and Subdomains: Teaches how domain infrastructure supports identification, correlation, and online attribution.
• Module 14. Translation options: Addresses language barriers and translation support during online investigations.
• Module 15. Phone Numbers and Info: Covers phone based OSINT and the investigative value of telecom related identifiers.
• Module 16. Public Records Searches: Trains investigators to incorporate public records into online intelligence work.
Phase 4. Online Platforms, Media, and Specialized Evidence Types
• Module 17. Social Media Sites: Covers social media as a major OSINT environment for identification, activity mapping, and evidence collection.
• Module 18. The Storytelling Power of Images: Teaches image based analysis, context extraction, and evidentiary interpretation.
• Module 19. Video Evidence Collection: Focuses on video acquisition, preservation, and analytical value.
• Module 20. Geolocation: Covers geolocation techniques and the interpretation of location based clues.
• Module 21. Tracking Transportation: Extends geolocation into transportation and movement analysis.
• Module 22. Tracking changes and getting alerts: Teaches investigators how to monitor changing online targets and preserve evolving evidence.
Phase 5. Tools, Frameworks, and Investigative Support Systems
• Module 23. 3rd Party Commercial Apps: Surveys commercial OSINT tools and how they fit into disciplined investigative workflows.
• Module 24. OSINT Frameworks (tools): Provides structured approaches to tool selection, workflow thinking, and investigative process support.
Phase 6. Analytical Risk, Emerging Challenges, and Specialized Topics
• Module 25. Misinformation, Disinformation, and Deception: Trains investigators to identify deception, manipulation, and false narratives in open sources.
• Module 26. AI Challenges: Covers the role of AI in OSINT, along with risks, distortion, and verification concerns.
• Module 27. Cryptocurrency: Introduces cryptocurrency as an OSINT and investigative topic with identification and attribution relevance.
Phase 7. Reporting, Case Integration, and Investigative Maturity
• Module 28. Reporting and Actionable Intelligence: Teaches how to turn collected information into structured findings and usable intelligence.
• Module 29. OSINT Case Studies: The True Crime Thrillers of Digital Investigations: Applies the course to realistic case based investigative scenarios.
• Module 30. Unraveling the Intricacies of Digital Forensics: Connects OSINT work to broader forensic and investigative practice.
• Module 31. Practicing OSINT and Resources: Reinforces continued practice, investigator growth, and ongoing resource development.
—
Meet Your Instructor: Erfan Tighzan
Erfan Tighzan brings a rare combination of lived operational awareness, technical depth, and intelligence driven thinking to the CSI Linux OSINT Masterclass: Uncover Hidden Intelligence & Digital Footprints. With roots in aerospace engineering and a career path shaped by real world upheaval, Erfan transitioned into intelligence analysis, cyber threat work, and penetration testing with a focus on the Middle East and the complex realities of modern conflict, security, and digital exposure. His work draws from OSINT, GEOINT, SIGINT, SOCINT, SDR analysis, ADS-B tracking, HFGCS monitoring, and operational security practices forged not as abstract theory, but as practical necessity. He is also a published author and co-author of The Grand Manifesto of OSINT, a CSI Linux linked handbook dedicated to lawful, ethical, and disciplined intelligence practice.
In this masterclass, Erfan teaches OSINT the way it is meant to be practiced: not as casual internet searching, but as a disciplined craft of collecting, validating, preserving, and interpreting digital traces that others overlook. His instruction is shaped by a blend of technical skill, geopolitical understanding, and a relentless respect for OPSEC, deception awareness, and evidentiary discipline. That perspective aligns closely with the themes reflected in The Grand Manifesto of OSINT, which covers anonymity, preserving online evidence, domains, personas, imagery, transportation tracking, cryptocurrency, AI, deception, and case driven investigative thinking. For investigators, analysts, journalists, and security professionals, Erfan brings a teaching style grounded in reality, shaped by pressure, and focused on turning scattered online fragments into meaningful, actionable intelligence.
